前言
为了让应用程序可以直接调用su执行系统命令和获取root权限,本文基于Purple Pi OH主板的Android SDK,介绍如果修改和编译一个root版本的Android11系统,以下为sdk源码修改方法。
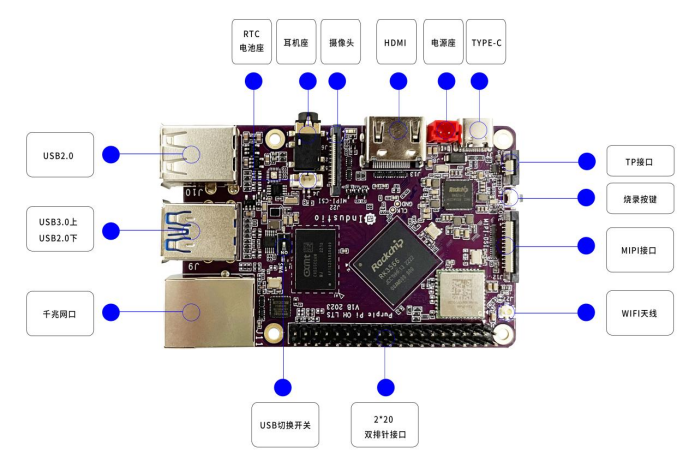
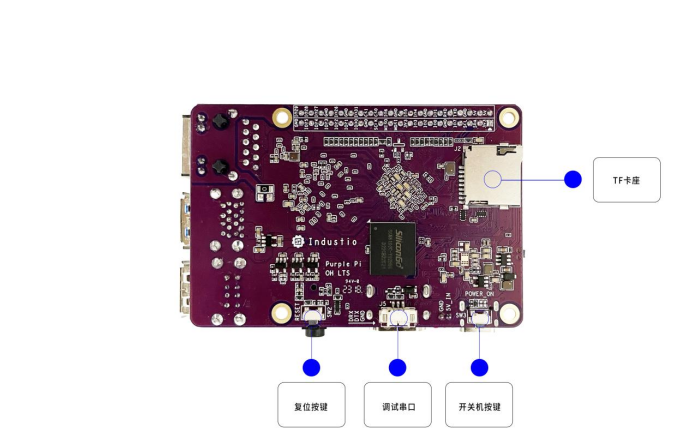
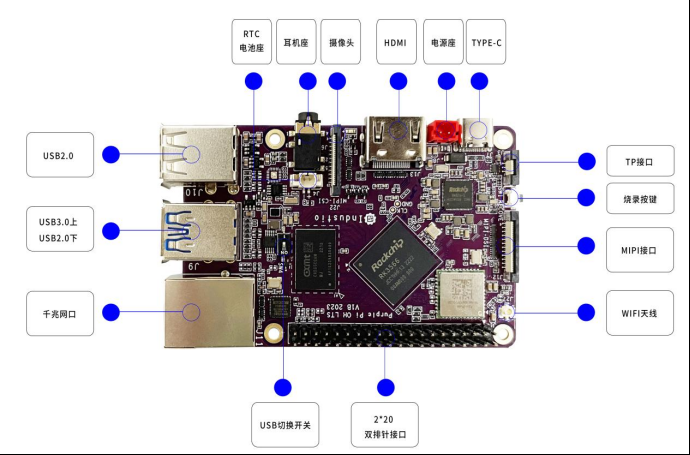
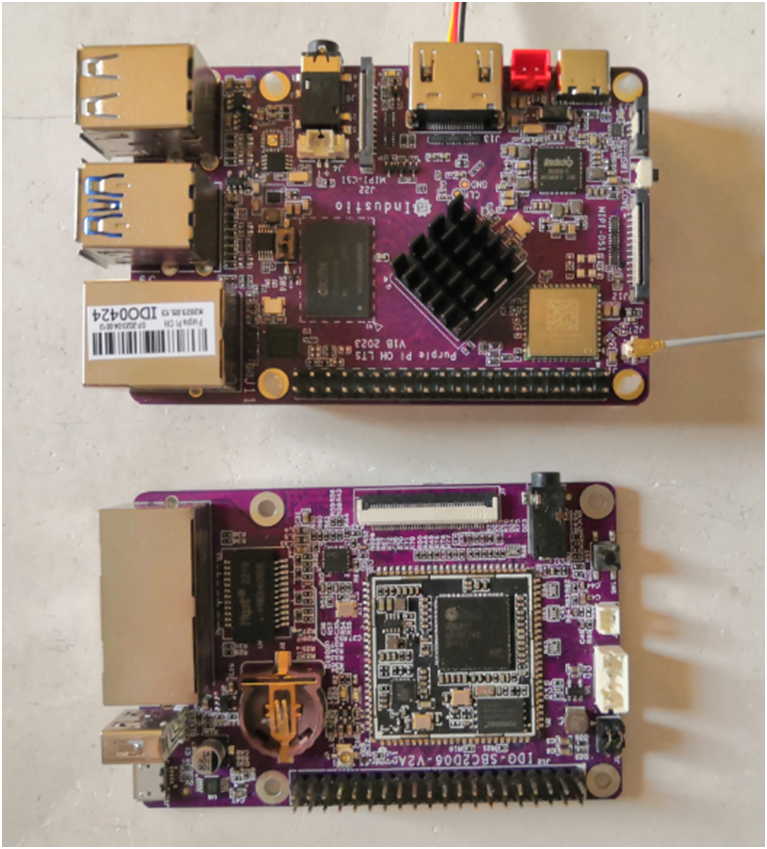
Purple Pi OH作为一款兼容树莓派的开源主板,采用瑞芯微RK3566 (Cortex-A55) 四核64位超强CPU,主频最高达1.8 GHz,算力高达1Tops,支持INT8/INT16,支持TensorFlow/MXNet/PyTorch/Caffe框架,多路视频输出和输入,支持4K、H.265/H.264视频解码,接口丰富。
玩法丰富,支持OpenHarmony、Ubuntu、Debian、Android等多种系统,提供丰富开源资料。
关闭selinux
device/rockchip/common/BoardConfig.mk
diff --git a/device/rockchip/common/BoardConfig.mkb/device/rockchip/common/BoardConfig.mk indexe03c54f6a0..4fc6dc9868 100755 --- a/device/rockchip/common/BoardConfig.mk +++ b/device/rockchip/common/BoardConfig.mk @@ -59,7+59,7@@ BOARD_BOOT_HEADER_VERSION ?= 2 BOARD_MKBOOTIMG_ARGS := BOARD_PREBUILT_DTBOIMAGE ?= $(TARGET_DEVICE_DIR)/dtbo.img BOARD_ROCKCHIP_VIRTUAL_AB_ENABLE ?= false -BOARD_SELINUX_ENFORCING ?= true +BOARD_SELINUX_ENFORCING ?= false # Use the non-open-sourceparts, ifthey're present
注释用户组权限检测
system/extras/su/su.cpp
diff --git a/system/extras/su/su.cpp b/system/extras/su/su.cpp index 1a1ab6bf40..af3d2a68c7 100644 --- a/system/extras/su/su.cpp +++ b/system/extras/su/su.cpp @@ -80,8+80,8@@ voidextract_uidgids(constchar* uidgids, uid_t* uid, gid_t* gid, gid_t* gids, i } intmain(intargc, char** argv){ - uid_tcurrent_uid = getuid(); - if(current_uid != AID_ROOT && current_uid != AID_SHELL) error(1, 0, "not allowed"); + //uid_t current_uid = getuid(); + //if (current_uid != AID_ROOT && current_uid != AID_SHELL) error(1, 0, "not allowed"); // Handle -h and --help. ++argv;给su文件默认授予root权限
system/core/libcutils/fs_config.cpp
diff --git a/system/core/libcutils/fs_config.cpp b/system/core/libcutils/fs_config.cpp index 5805a4d19b..92e93e76ff 100644 --- a/system/core/libcutils/fs_config.cpp +++ b/system/core/libcutils/fs_config.cpp @@ -188,7+188,7@@ staticconststructfs_path_configandroid_files[] = { // the following two files are INTENTIONALLY set-uid, but they // are NOT included on user builds. { 06755, AID_ROOT, AID_ROOT, 0, "system/xbin/procmem"}, - { 04750, AID_ROOT, AID_SHELL, 0, "system/xbin/su"}, + { 06755, AID_ROOT, AID_SHELL, 0, "system/xbin/su"}, // the following files have enhanced capabilities and ARE included // in user builds.
frameworks/base/core/jni/com_android_internal_os_Zygote.cpp
diff --git a/frameworks/base/core/jni/com_android_internal_os_Zygote.cpp b/frameworks/base/core/jni/com_android_internal_os_Zygote.cpp
index 9eede83e21..d161e6fad3 100644
--- a/frameworks/base/core/jni/com_android_internal_os_Zygote.cpp
+++ b/frameworks/base/core/jni/com_android_internal_os_Zygote.cpp
@@ -656,7+656,7@@ staticvoidEnableKeepCapabilities(fail_fn_t fail_fn) {
}
staticvoidDropCapabilitiesBoundingSet(fail_fn_t fail_fn) {
- for(inti = 0; prctl(PR_CAPBSET_READ, i, 0, 0, 0) >= 0; i++) {;
+/* for (int i = 0; prctl(PR_CAPBSET_READ, i, 0, 0, 0) >= 0; i++) {;
if (prctl(PR_CAPBSET_DROP, i, 0, 0, 0) == -1) {
if (errno == EINVAL) {
ALOGE("prctl(PR_CAPBSET_DROP) failed with EINVAL. Please verify "
@@ -665,7 +665,7 @@ static void DropCapabilitiesBoundingSet(fail_fn_t fail_fn) {
fail_fn(CREATE_ERROR("prctl(PR_CAPBSET_DROP, %d) failed: %s", i, strerror(errno)));
}
}
- }
+ }*/
}
kernel/security/commoncap.c
diff --git a/kernel/security/commoncap.c b/kernel/security/commoncap.c
index 876cfe01d9..ce87b1b780 100644
--- a/kernel/security/commoncap.c
+++ b/kernel/security/commoncap.c
@@ -1166,12+1166,12@@ intcap_task_setnice(struct task_struct *p, intnice)
staticintcap_prctl_drop(unsignedlongcap)
{
structcred*new;
-
+/*
if (!ns_capable(current_user_ns(), CAP_SETPCAP))
return -EPERM;
if (!cap_valid(cap))
return -EINVAL;
-
+*/
new= prepare_creds();
if(!new)
return-ENOMEM;
编译镜像
修改后需要重新编译内核和AOSP,Android编译需要选择rk3566_r-userdebug版本
sourcebuild/envsetup.sh lunch rk3566_r-userdebug检测验证root是否成功
可在应用程序中调用 /system/xbin/su来测试系统是否root成功
publicstaticvoidRootCommand() {
Process process = null;
try{
process = Runtime.getRuntime().exec("/system/xbin/su");
process.waitFor();
} catch(IOException | InterruptedException e) {
e.printStackTrace();
} finally{
if(process != null) {
process.destroy();
}
}
}
root的系统可正常执行,而非root的系统会提示没有权限
java.io.IOException: Cannot run program "/system/xbin/su": error=13, Permission denied
审核编辑:汤梓红
-
Android
+关注
关注
12文章
3935浏览量
127339 -
cpu
+关注
关注
68文章
10854浏览量
211574 -
主板
+关注
关注
53文章
1875浏览量
70764 -
root
+关注
关注
1文章
86浏览量
21388 -
树莓派
+关注
关注
116文章
1706浏览量
105607
原文标题:【技术分享】Purple Pi OH Android11 ROOT 方法
文章出处:【微信号:industio,微信公众号:深圳触觉智能】欢迎添加关注!文章转载请注明出处。
发布评论请先 登录
相关推荐
【触觉智能 Purple Pi OH 开发板体验】+ 熟悉PurplePiOH编译固件
[触觉智能 Purple Pi OH开发板体验] 二.RK3566运行Android11
【触觉智能 Purple Pi OH 开发板体验】检测Android系统的完备性
Purple Pi OH Android11 ROOT方法
Purple Pi OH 开发板体验:应用开发的问题
Purple Pi OH Android11 ROOT 方法

瑞芯微RK3566鸿蒙开发板Android11修改第三方输入法为默认输入法
瑞芯微RK3566/RK3568 Android11使用OTA升级固件方法,深圳触觉智能鸿蒙开发板演示,备战第九届华为ICT大赛
瑞芯微RK3566/RK3568 Android11下该如何默认屏蔽导航栏/状态栏?看这篇文章就懂了




 Purple Pi OH Android11 ROOT方法
Purple Pi OH Android11 ROOT方法









评论